Qatar RAT 2026
The cybersecurity landscape continues to evolve rapidly, and remote access tools remain one of the most powerful — and dangerous — technologies in the digital ecosystem. Qatar RAT 2026 has recently surfaced as a highly advanced remote administration framework, raising serious security concerns due to its extensive control capabilities and intrusive features.
This article provides an in-depth technical breakdown of Qatar RAT 2026, analyzing its interface structure, functional modules, operational capabilities, and the cybersecurity risks associated with such tools.
🔍 What is Qatar RAT 2026?
Qatar RAT 2026 appears to be a next-generation Remote Administration Tool (RAT) designed to control and manage remote systems. While remote administration software can be used legitimately for IT support and enterprise management, tools with excessive surveillance and destructive capabilities often fall into the malware category when deployed without consent.
From its interface structure, Qatar RAT 2026 is designed for centralized control of multiple remote machines, offering detailed system insights and extensive manipulation options.
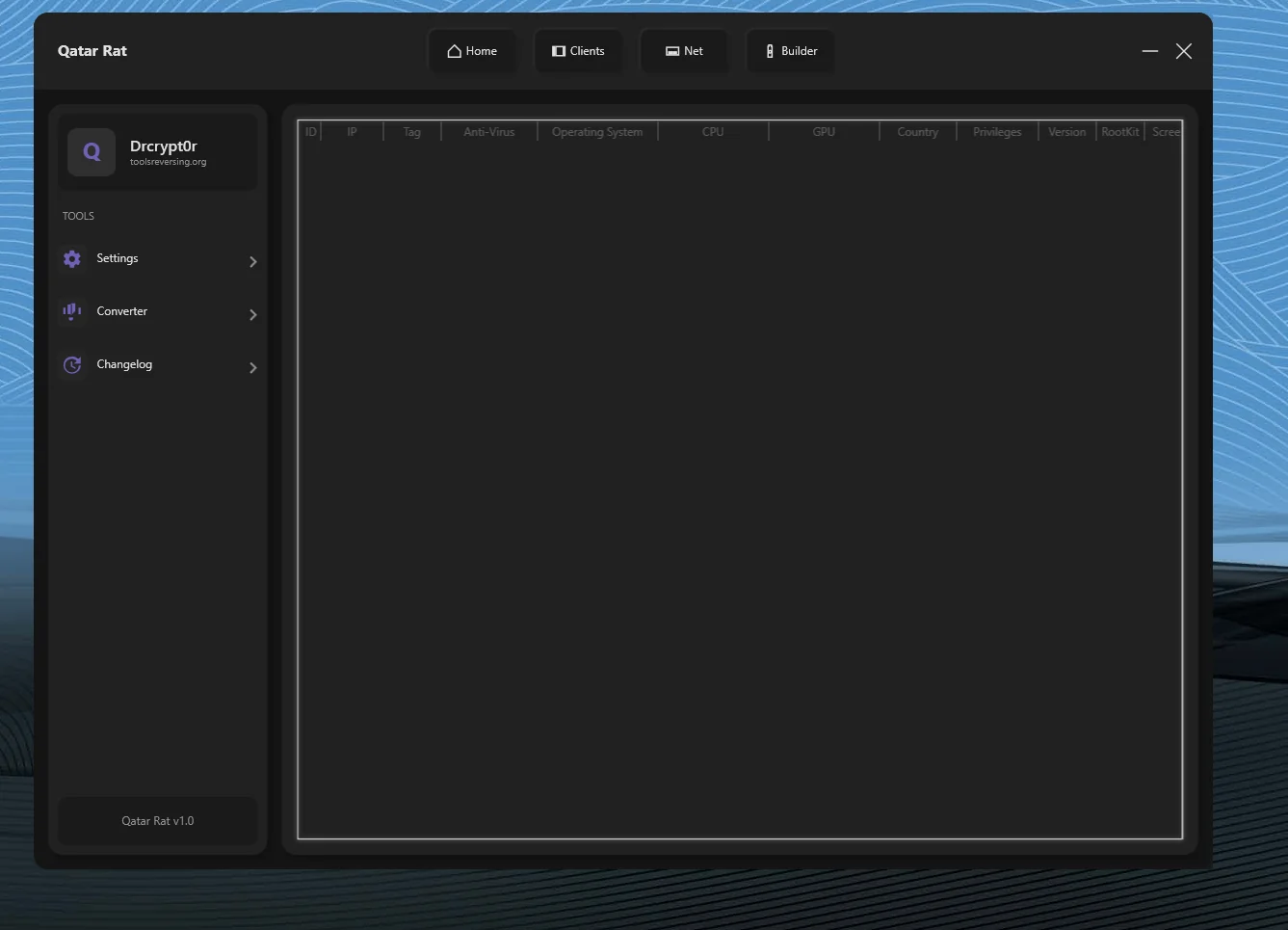
🖥️ Core Interface Structure and Design
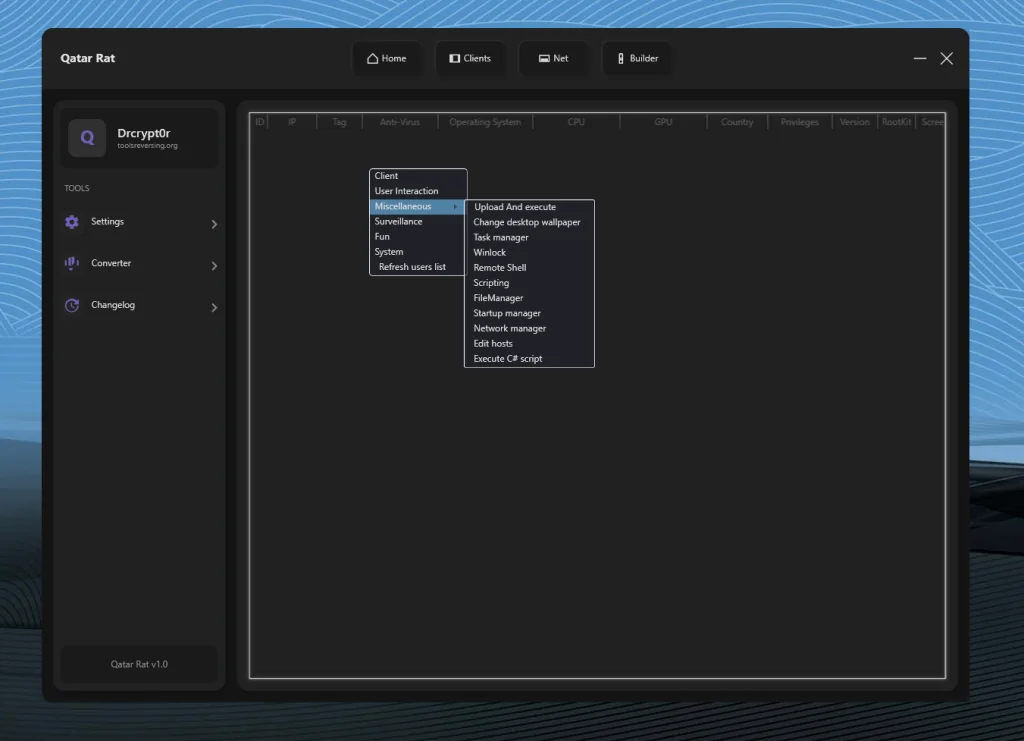
The software appears to follow a modular dashboard layout optimized for workflow efficiency. The main sections typically include:
- 🏠 Home Dashboard
- 👥 Clients Panel
- 🌐 Network Management
- 🛠️ Builder Module
- ⚙️ Settings & Utility Tools
The clean layout suggests that the tool is designed to manage large numbers of remote connections simultaneously, making it scalable for broader operations.
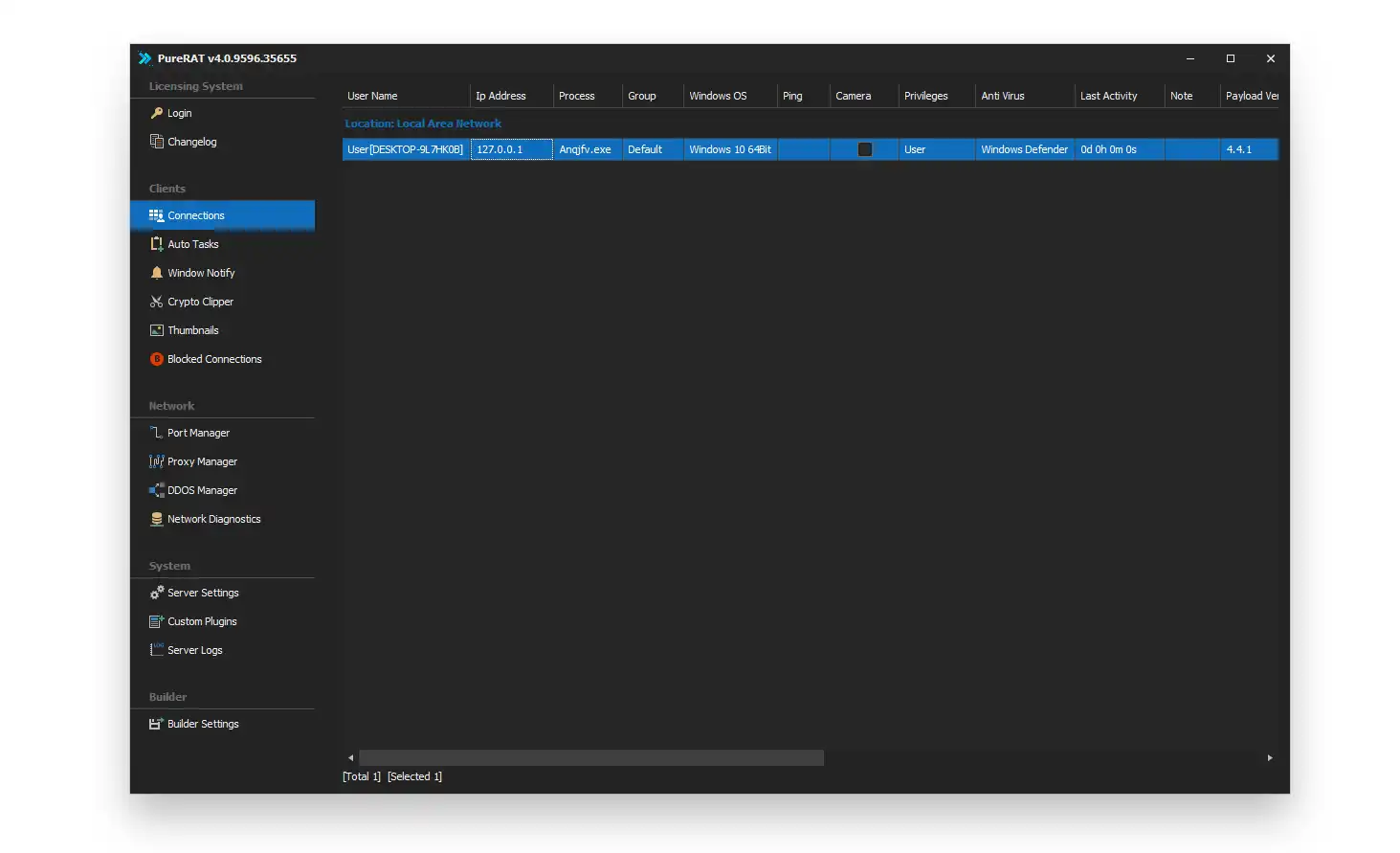
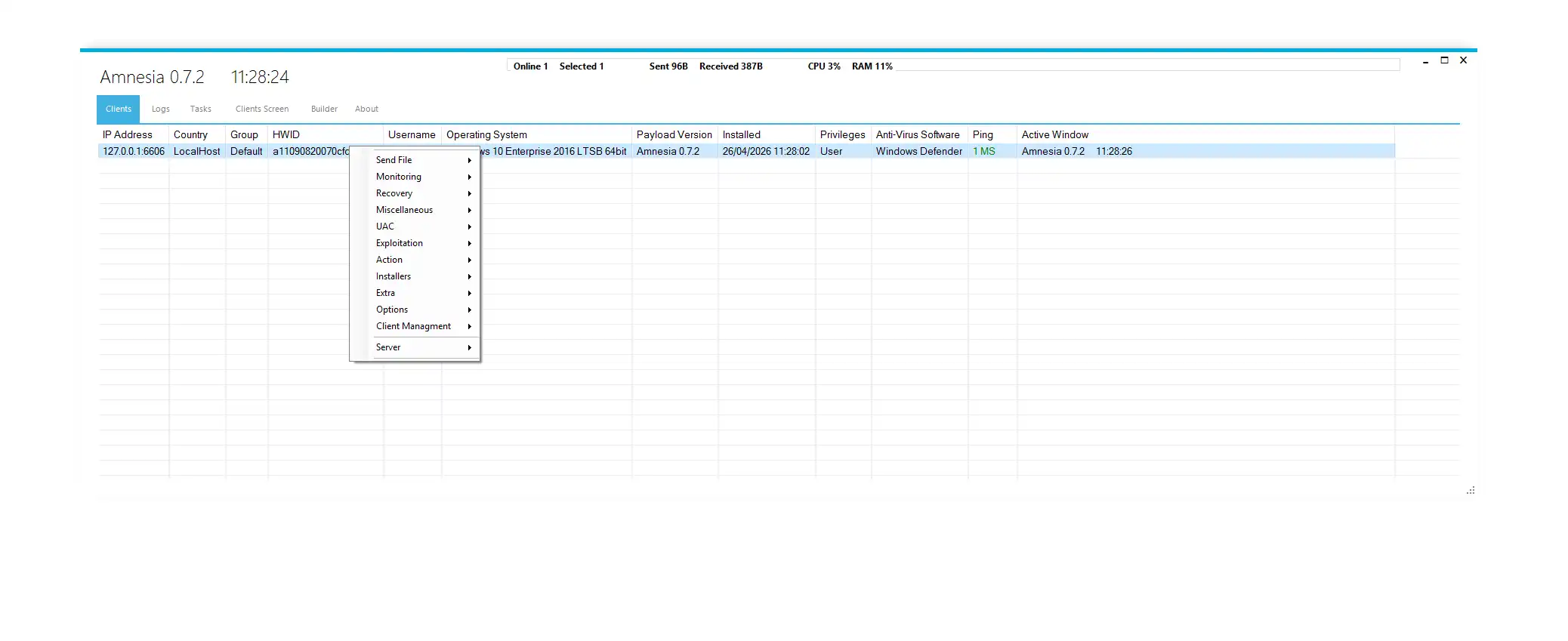
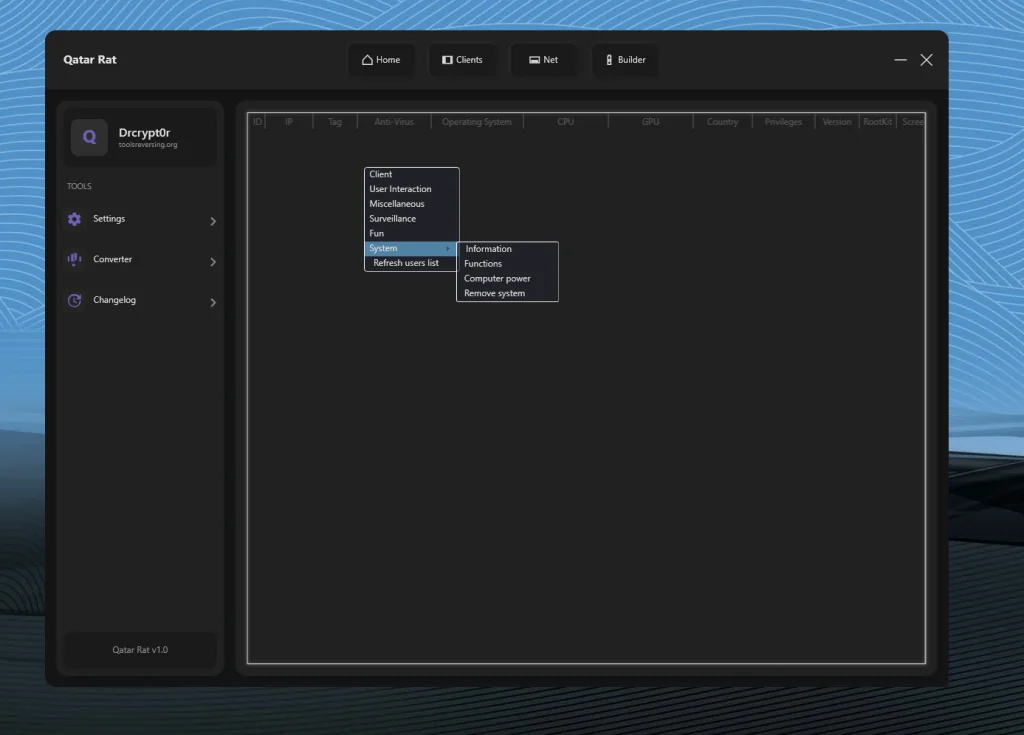
📊 Advanced Client Monitoring Capabilities
One of the most powerful components of Qatar RAT 2026 is its client management table. Each connected system displays detailed information such as:
- 🆔 Unique Client ID
- 🌍 IP Address
- 🗺️ Country Location
- 💻 Operating System Version
- ⚙️ CPU & GPU Details
- 🔐 User Privileges
- 🛡️ Antivirus Status
- 🕵️ Rootkit Presence
- 🔢 Installed Version
This level of visibility allows operators to quickly assess system defenses, privilege levels, and hardware specifications.
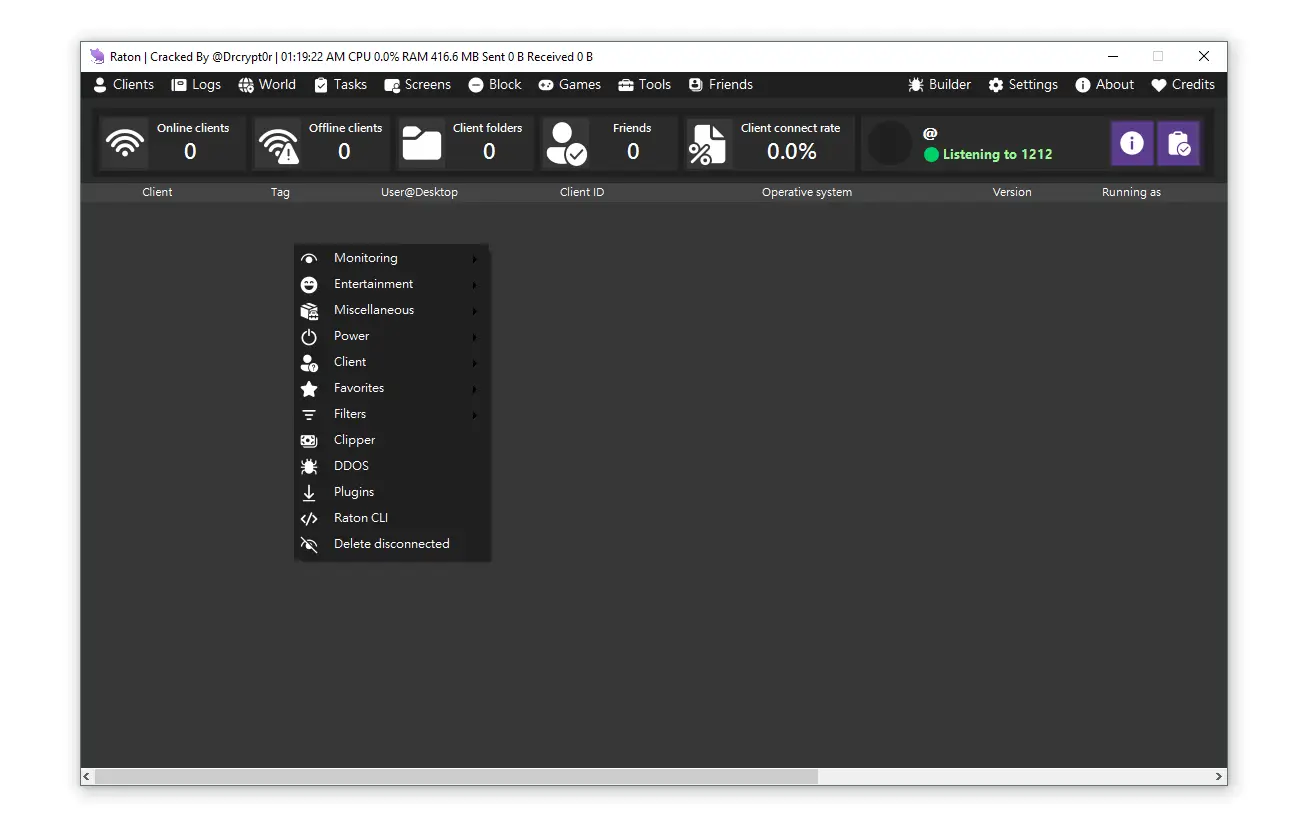
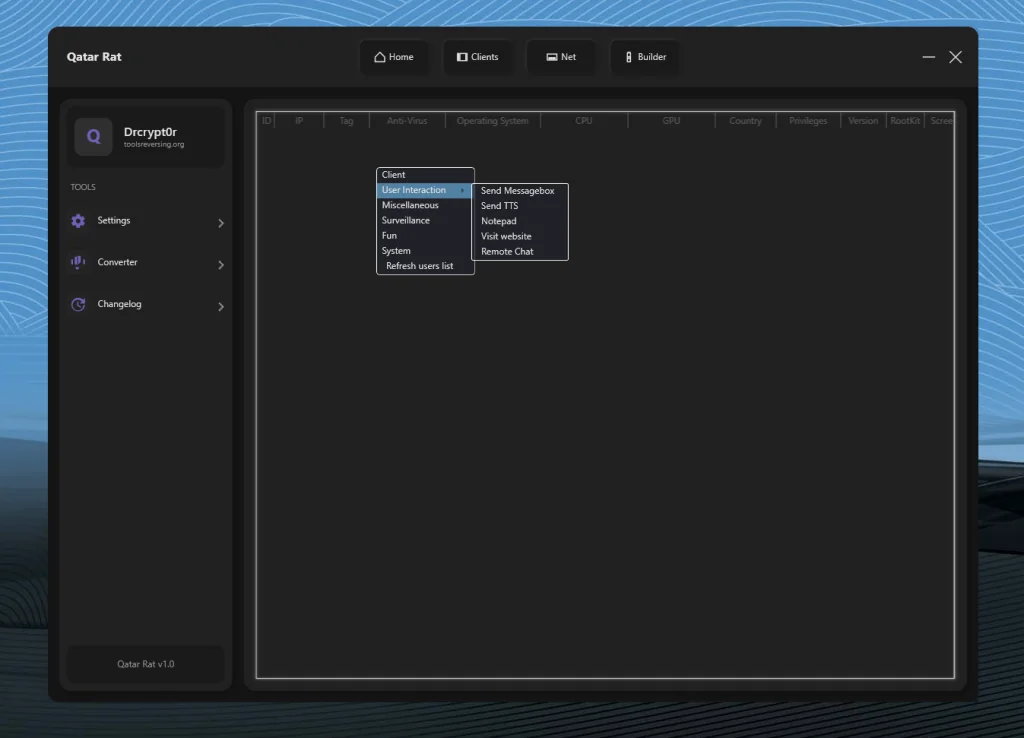
💬 Remote Interaction Features
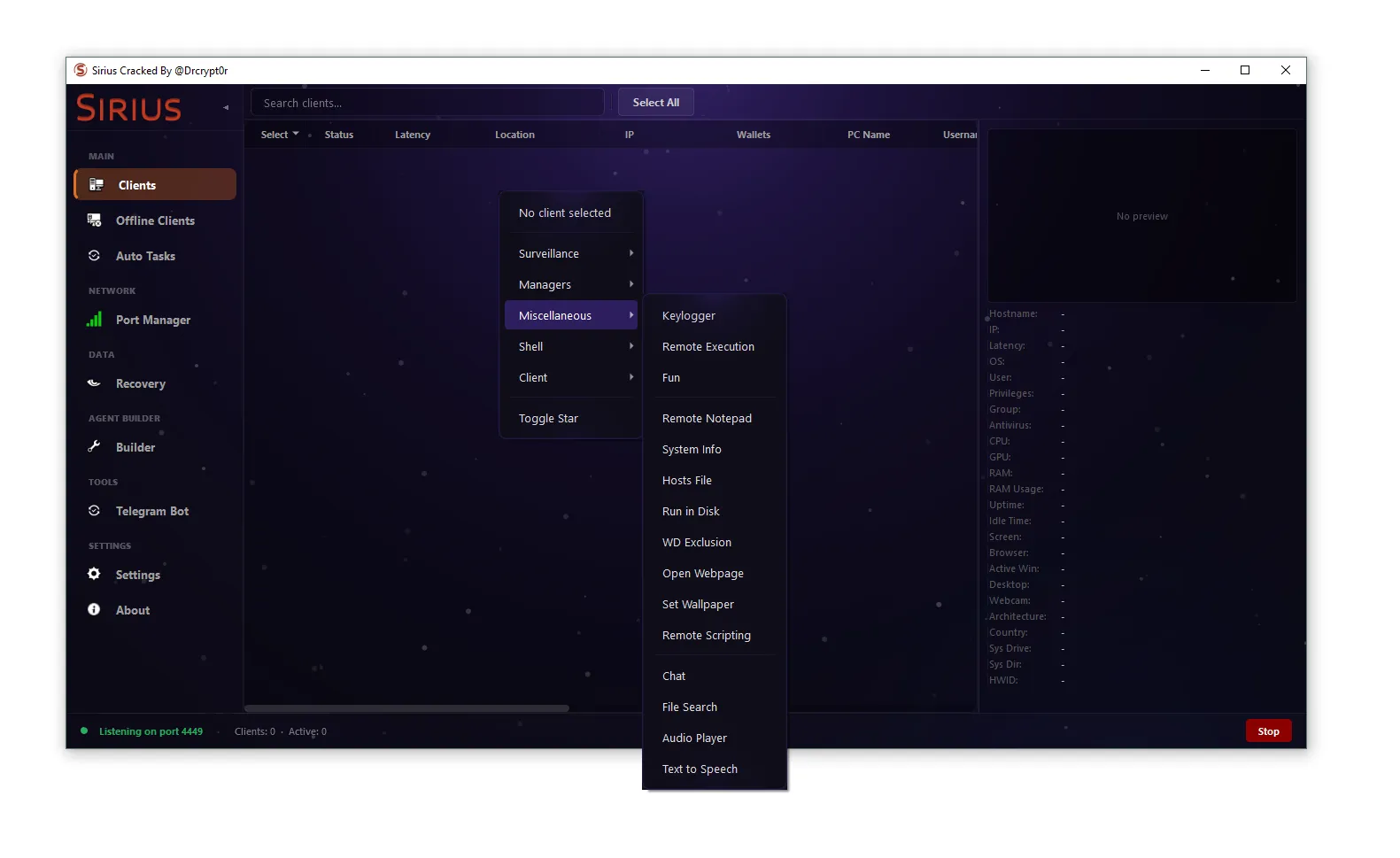
Under its interaction module, Qatar RAT 2026 enables direct engagement with the remote user environment. These features may include:
- 📩 Sending message pop-ups
- 🔊 Text-to-speech execution
- 📝 Opening text editors remotely
- 🌐 Forcing website visits
- 💬 Remote chat sessions
While these capabilities may resemble legitimate support tools, they can also be exploited for phishing, intimidation, or social engineering attacks.
⚡ System Control and Execution Modules
The system management capabilities of Qatar RAT 2026 significantly increase its threat level. Key features include:
🖥️ Remote Shell Access
- ⌨️ Execute command-line instructions on the remote machine.
📁 File Manager
- 📂 Browse system directories
- ⬆️ Upload files
- ⬇️ Download files
- ❌ Delete or modify data
🧩 Script Execution
- 📜 Run custom scripts
- 🚀 Deploy additional payloads
- 📤 Extract sensitive information
🔄 Startup Manager
- 🔁 View programs running at boot
- 📌 Establish persistence mechanisms
🌐 Network Manager
- 📡 Monitor active connections
- 🔍 Analyze network behavior
🧾 Hosts File Editing
- 🔀 Redirect web traffic
- 🎯 Manipulate domain resolution
📦 Upload and Execute
- 🧨 Deploy secondary malware
- 🔐 Deliver ransomware payloads
These features indicate that Qatar RAT 2026 can maintain deep and persistent control over infected systems.
🕶️ Surveillance and Intrusive Capabilities
A defining characteristic of high-risk RAT malware is its surveillance potential. Qatar RAT 2026 appears to include intrusive monitoring options that may allow:
- 👁️ Monitoring user activity
- 📊 Observing system behavior
- 🖥️ Gathering hardware data
- 🕵️ Maintaining stealth via rootkit integration
The possible presence of rootkit functionality significantly increases its danger, as it may conceal the malware from antivirus detection.
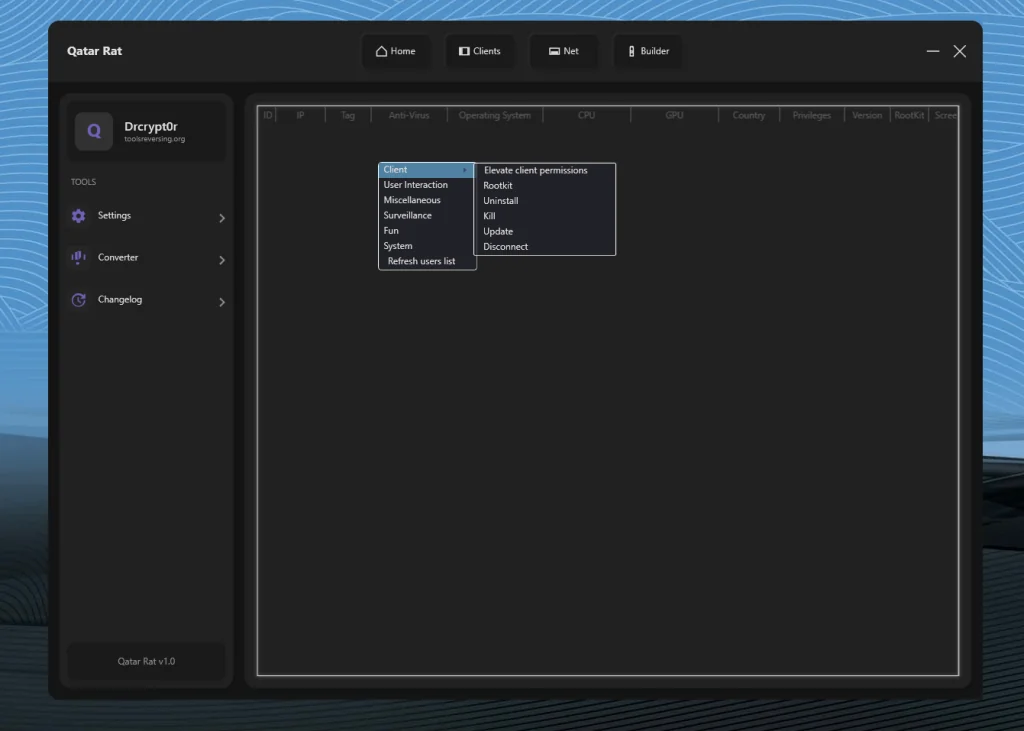
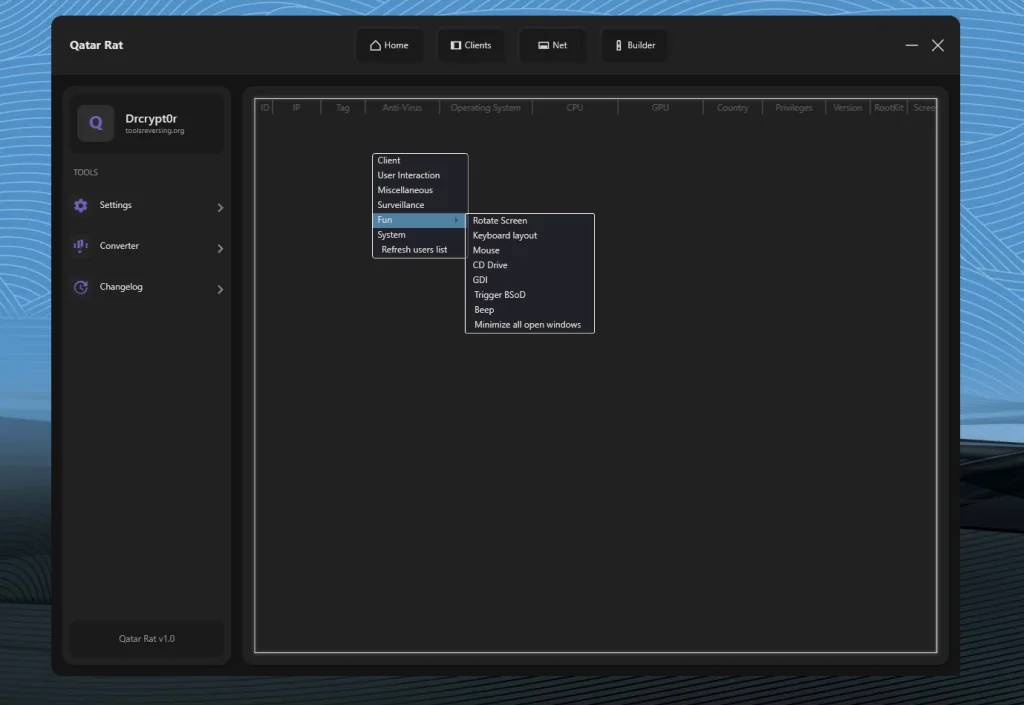
💣 Disruptive and Destructive Functions
Unlike legitimate enterprise remote tools, Qatar RAT 2026 reportedly includes disruptive system manipulation features such as:
- 💥 Triggering system crashes (BSoD)
- 🔄 Rotating the display screen
- ⌨️ Altering keyboard layout
- 🖱️ Controlling mouse behavior
- 🔔 Forcing system sounds
- 🔒 Locking the workstation
- 🗂️ Minimizing all windows
These features serve no professional administrative purpose and strongly suggest malicious intent when deployed covertly.
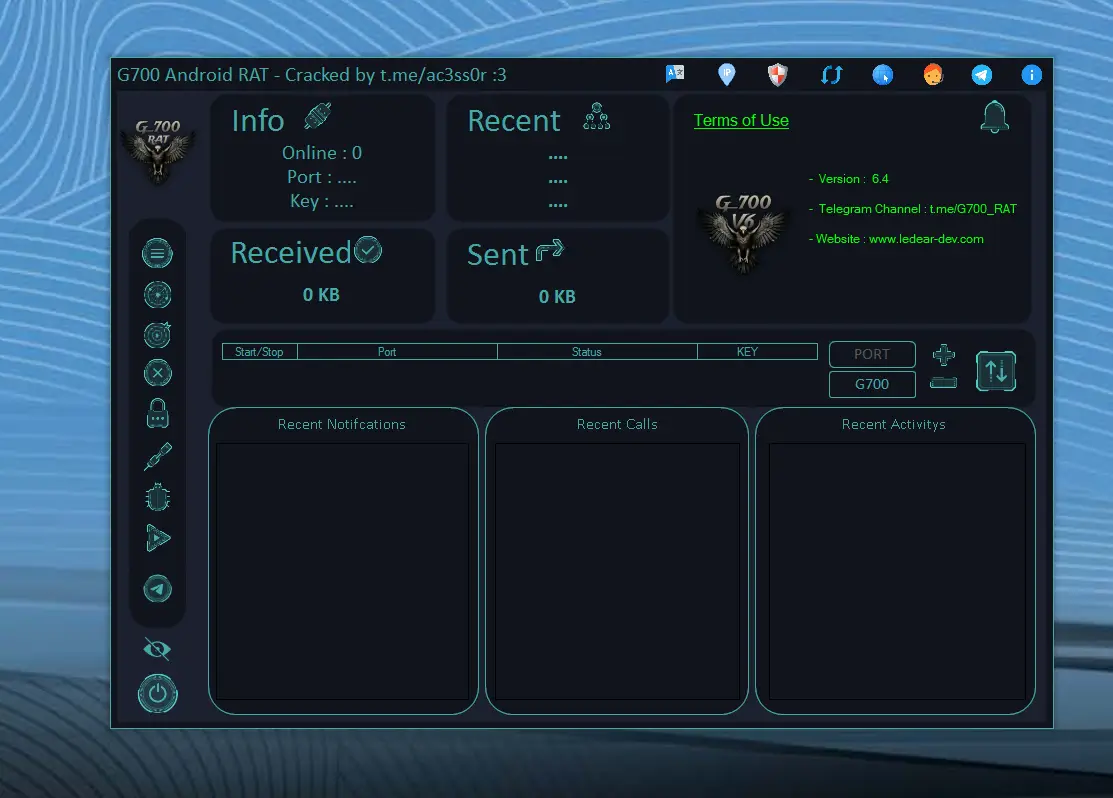
🏗️ Builder Module and Payload Customization
One of the most concerning elements of Qatar RAT 2026 is the apparent inclusion of a Builder module.
A builder typically allows operators to:
- 🧬 Generate customized payloads
- ⚙️ Configure connection settings
- 🎨 Modify executable icons
- 🔁 Adjust persistence options
- 🛡️ Apply obfuscation techniques
Customizable builders significantly increase the adaptability of malware, making detection more difficult for security systems.
🚨 Cybersecurity Risks of Qatar RAT 2026
If deployed maliciously, Qatar RAT 2026 poses several major risks:
🔓 1. Full Remote Compromise
- 🖥️ Complete device takeover
📤 2. Data Exfiltration
- 📂 Theft of sensitive documents
- 🔑 Extraction of stored credentials
🌐 3. Botnet Expansion
- 🤖 Integration into large attack networks
🔐 4. Ransomware Deployment
- 💰 Encryption-based extortion attacks
🕳️ 5. Persistent Backdoor Access
- 🔄 Long-term unauthorized system control
🛡️ Defensive Considerations for Security Professionals
Understanding tools like Qatar RAT 2026 is critical for cybersecurity defense strategies. Security teams should focus on:
- 🧠 Behavioral detection systems
- 🌍 Monitoring unusual outbound connections
- 📜 Detecting unauthorized script execution
- 🔎 Scanning for rootkit indicators
- ⬆️ Monitoring privilege escalation
- 🛡️ Implementing Endpoint Detection & Response (EDR)
Proactive monitoring and layered security architecture are essential to mitigate threats posed by advanced RAT frameworks.
Download Qatar RAT 2026
⚖️ Final Analysis: The Double-Edged Nature of Remote Access Tools
Qatar RAT 2026 represents a powerful and technically sophisticated remote control framework. While remote administration tools have legitimate applications, the combination of surveillance capabilities, destructive features, and customizable payload generation strongly positions this software within the high-risk malware category if used without authorization.
As cyber threats continue to evolve, tools like Qatar RAT 2026 highlight the ongoing arms race between attackers and defenders. Understanding their structure and capabilities is essential for building stronger cybersecurity defenses and reducing the risk of system compromise.