Malware
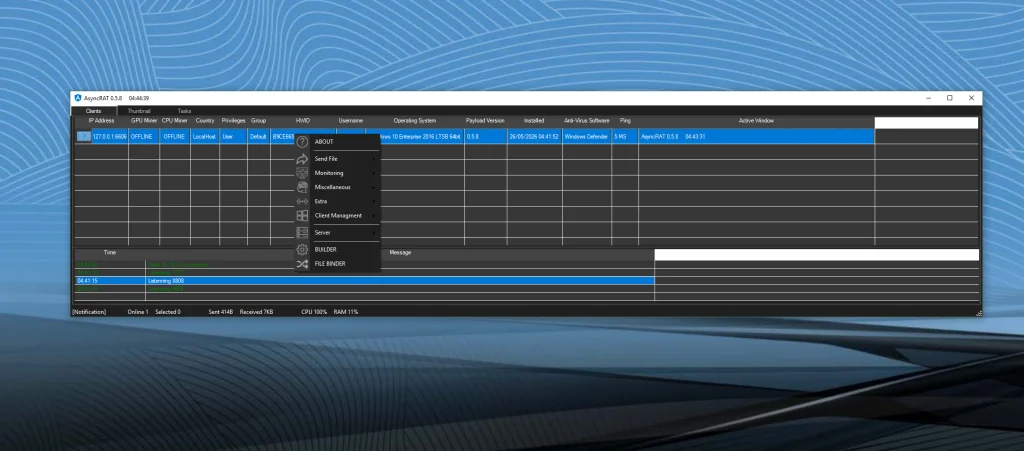
AsyncRAT v0.5.8 Cracked
🛡️ Technical Deep Dive: Analyzing AsyncRAT v0.5.8 Cracked Features In the modern cybersecurity landscape, Remote Access Trojans (RATs) continue to evolve into highly sophisticated malware frameworks capable of surveillance, credential…
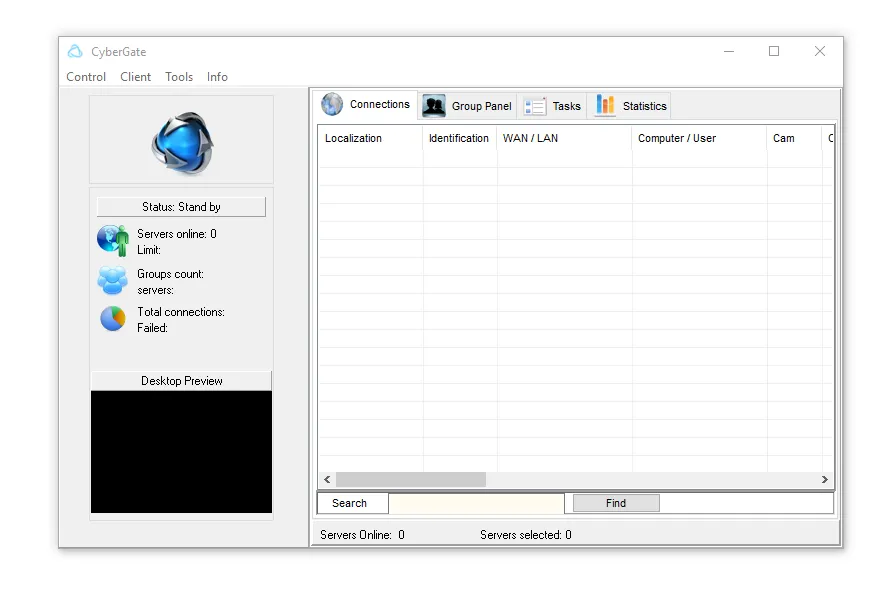
CyberGate v3.4.2.2
🛡️ CyberGate v3.4.2.2: A Look at a Historic Remote Access Trojan CyberGate v3.4.2.2 became one of the most recognized Remote Access Trojans (RATs) during the early era of modern cybercrime…
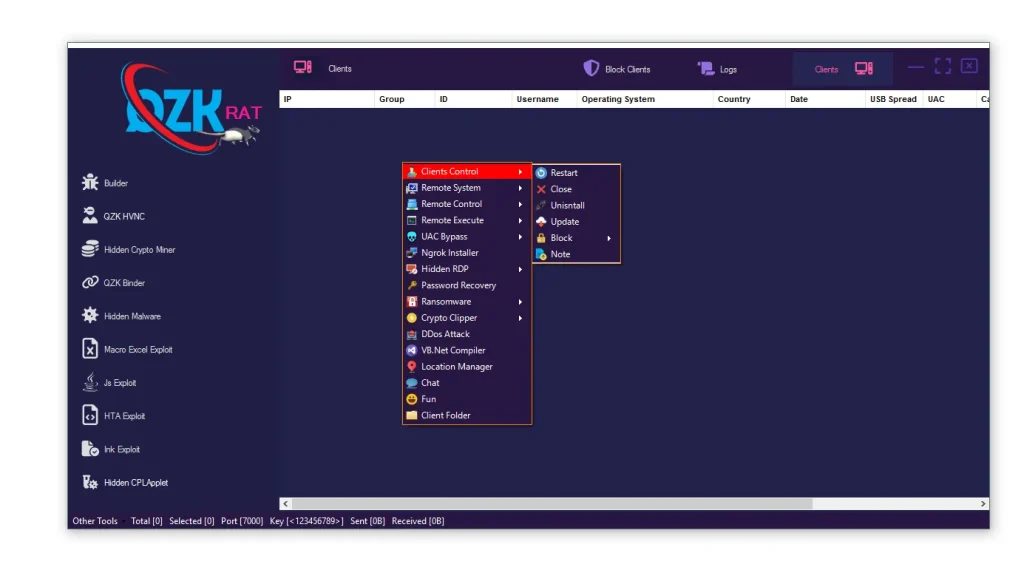
QZK RAT 2026
Introduction: What is QZK RAT 2026? QZK RAT 2026 is a modern modular Remote Access Trojan (RAT) framework designed to combine multiple cybercrime capabilities into a single malware management platform…
Crypter
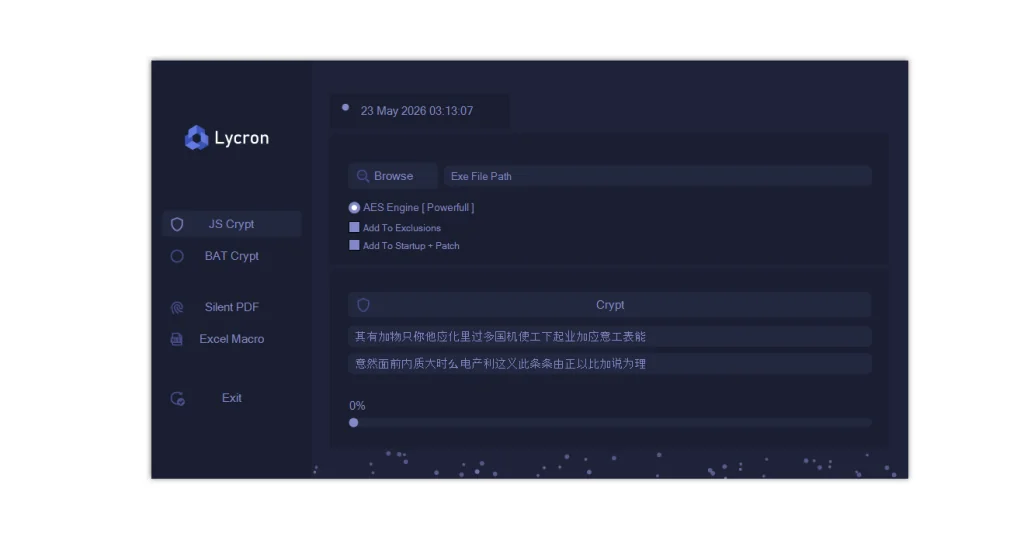
Lycron Crypter 2026 Cracked
Lycron Crypter 2026 Cracked The cybersecurity industry continues to evolve as both security researchers and cybercriminals develop more advanced technologies. In recent years, malware obfuscation tools have become increasingly common…
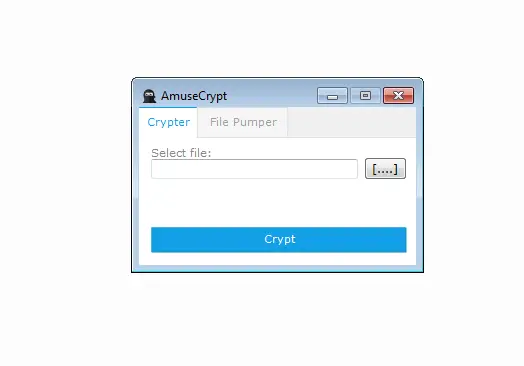
Amuse Crypt V 2.0
Amuse Crypt V 2.0
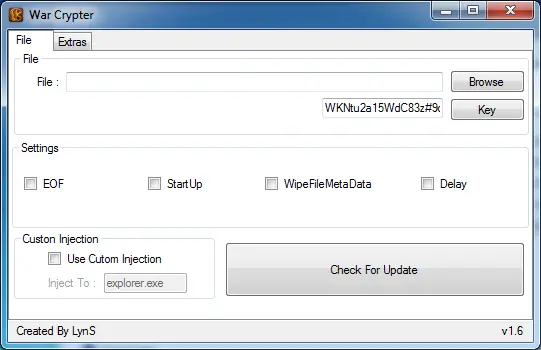
War Crypter 1.6
War Crypter 1.6 A simple free crypter with daily free refud
Binder
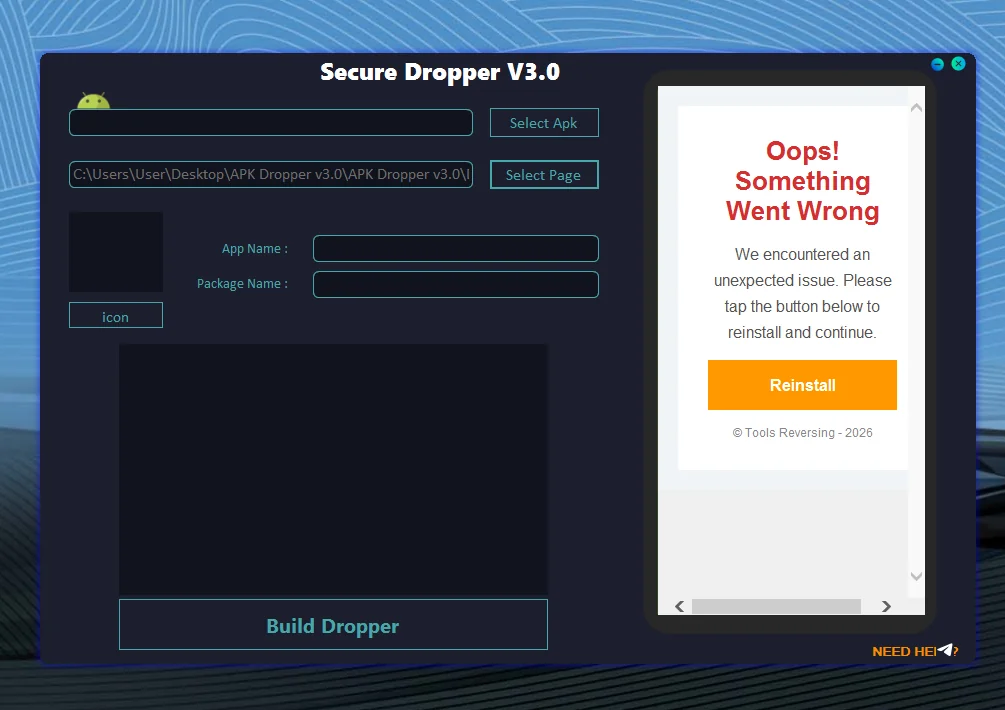
APK Dropper v3.0
📱 Introduction to APK Dropper v3.0 Malware Android devices rely on APK (Android Application Package) files to install applications. While most APK files are legitimate, cybercriminals sometimes misuse this format…
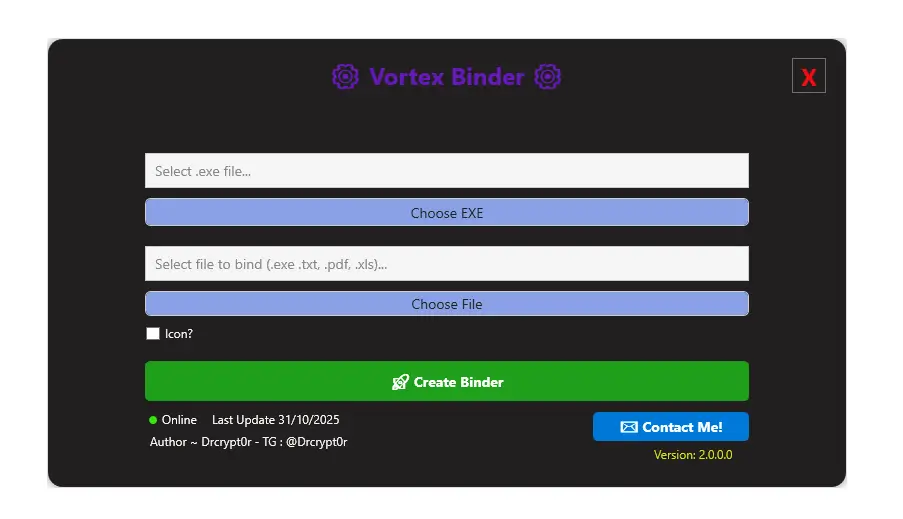
Vortex Binder 2.0
Vortex Binder 2.0 In the fast-paced world of software development, distributing applications seamlessly is a must. Enter Vortex Binder 2.0, a sleek, user-friendly tool designed to bind executable files (EXEs)…
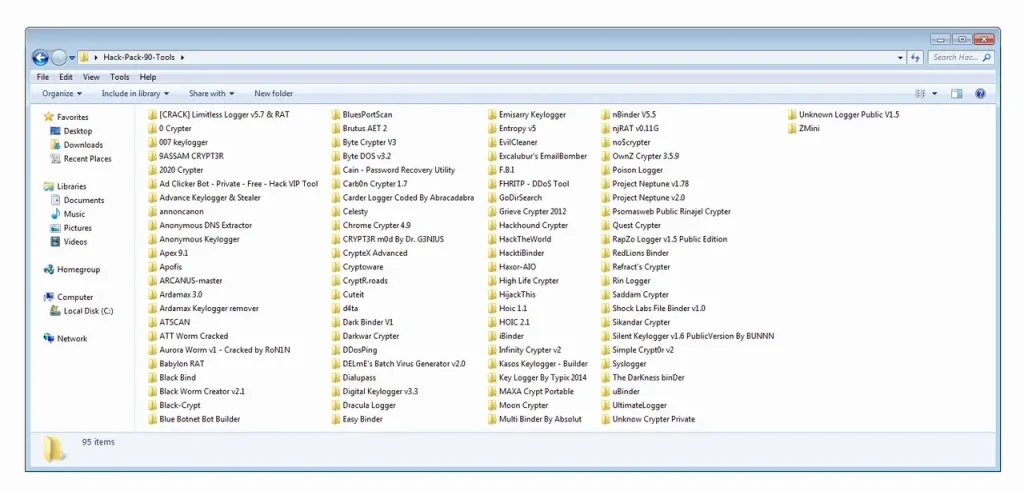
HACK PACK Crypters, Binders, Keyloggers and more
HACK PACK Crypters, Binders, Keyloggers and more
Bruter
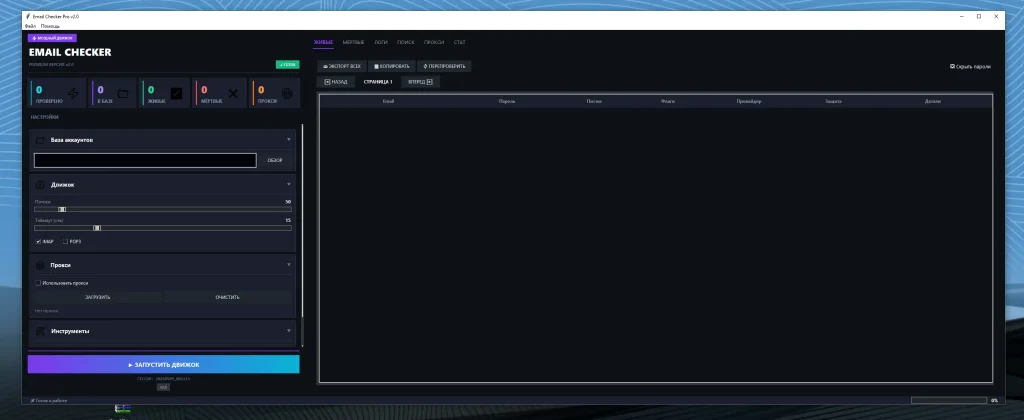
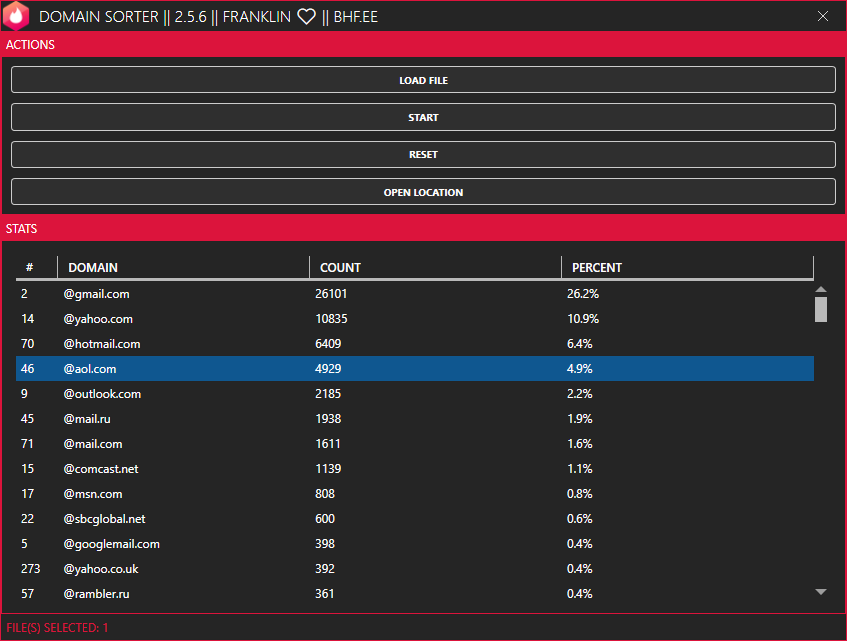
Mail Checker Pro v2.0
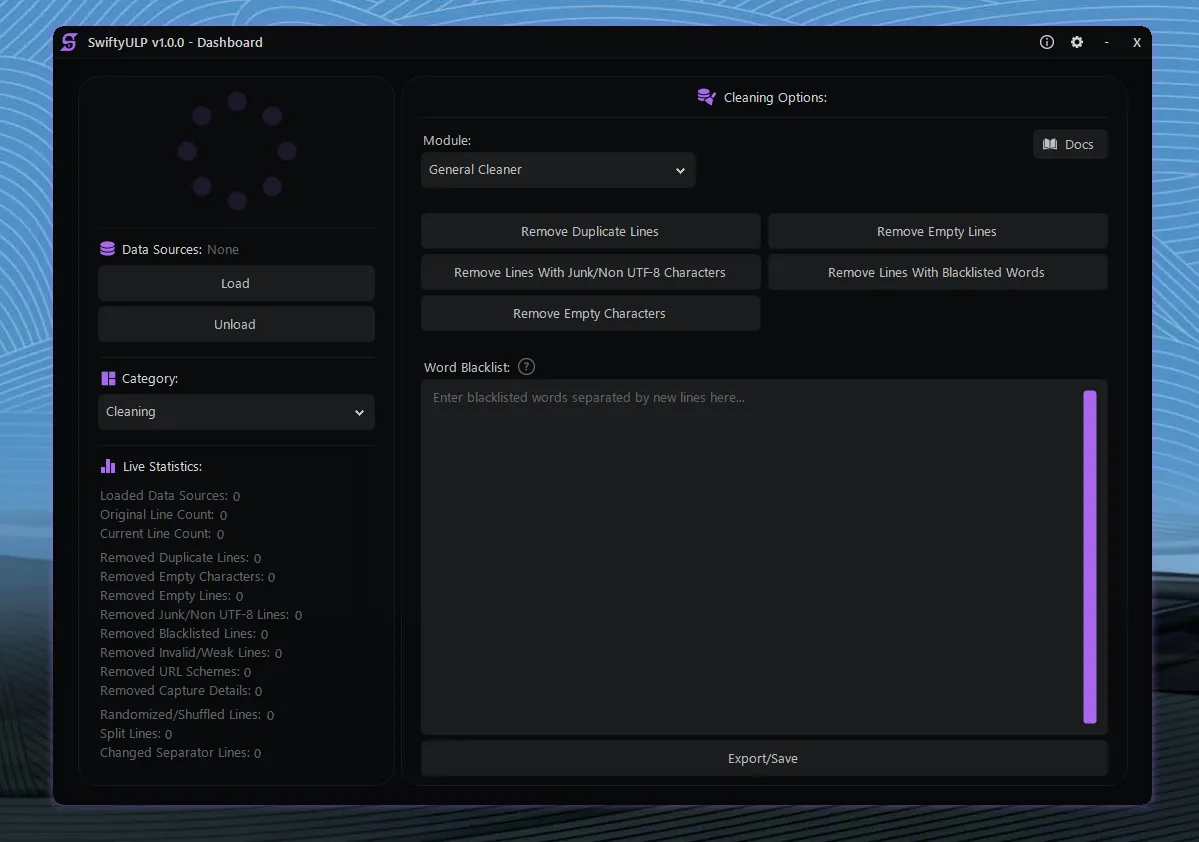
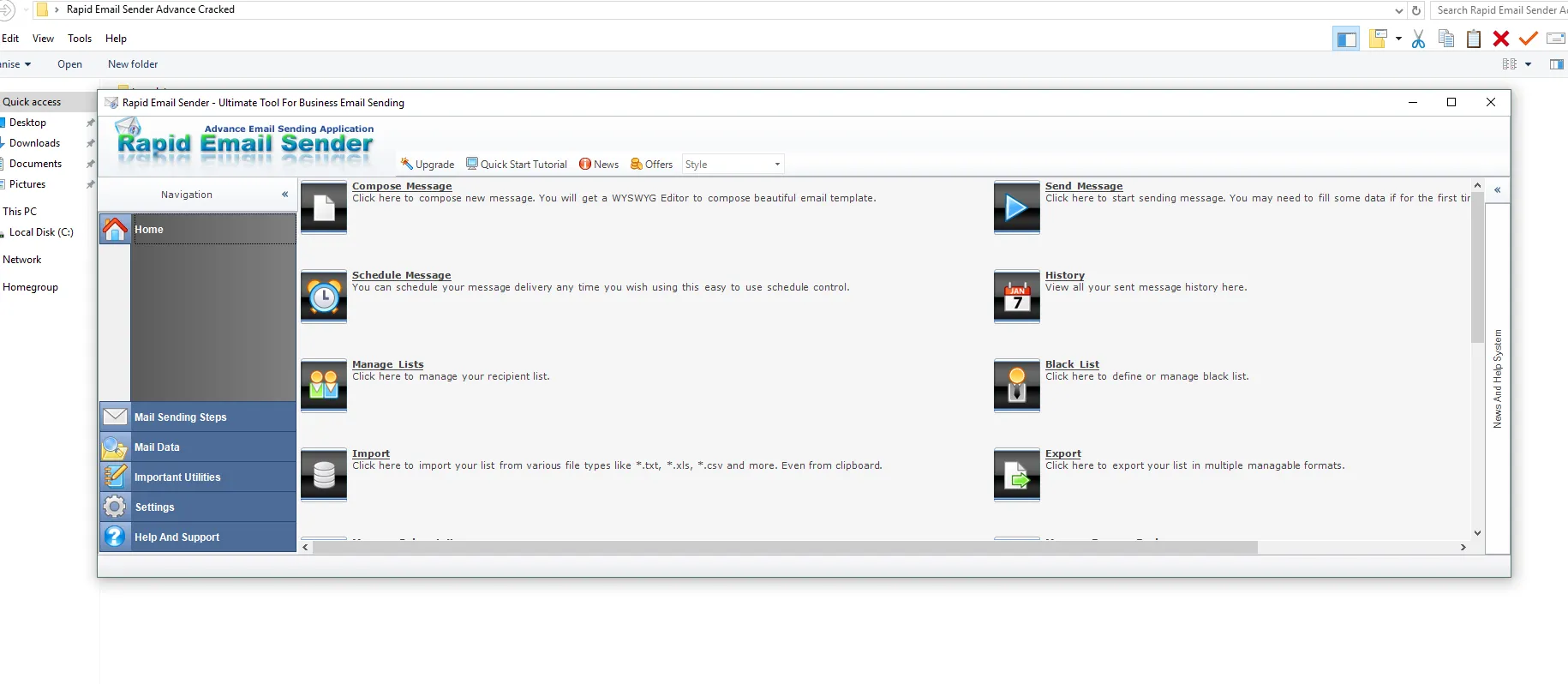
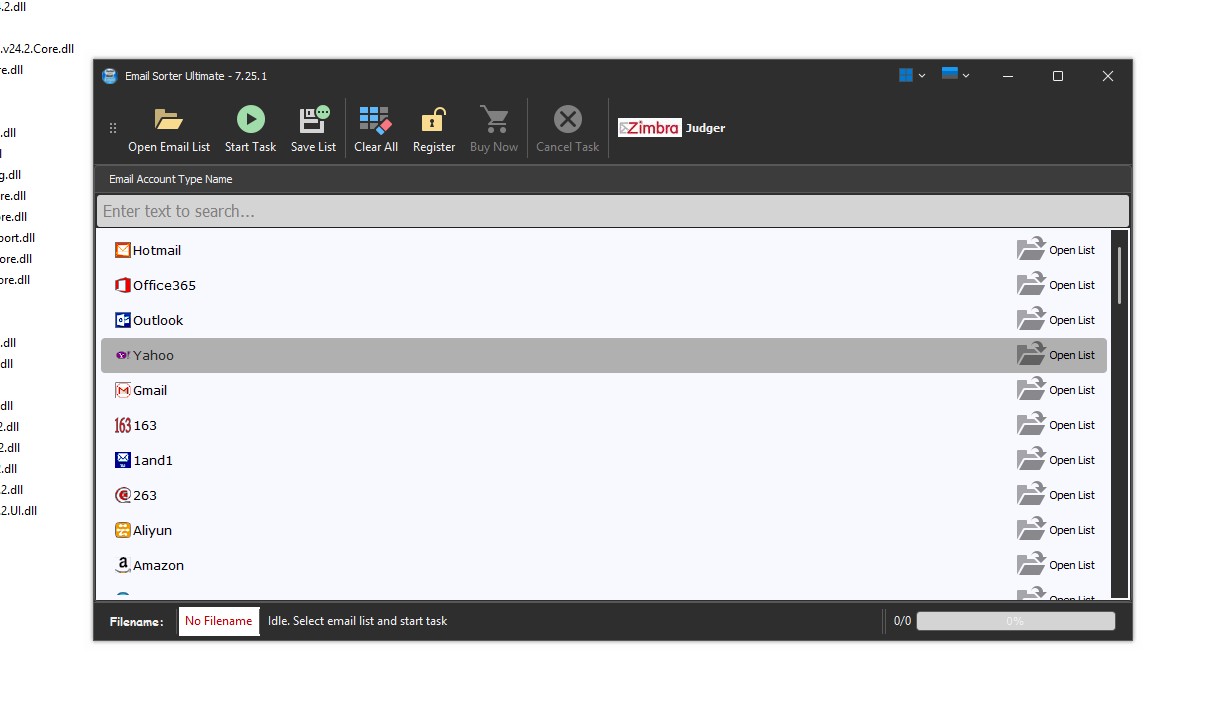
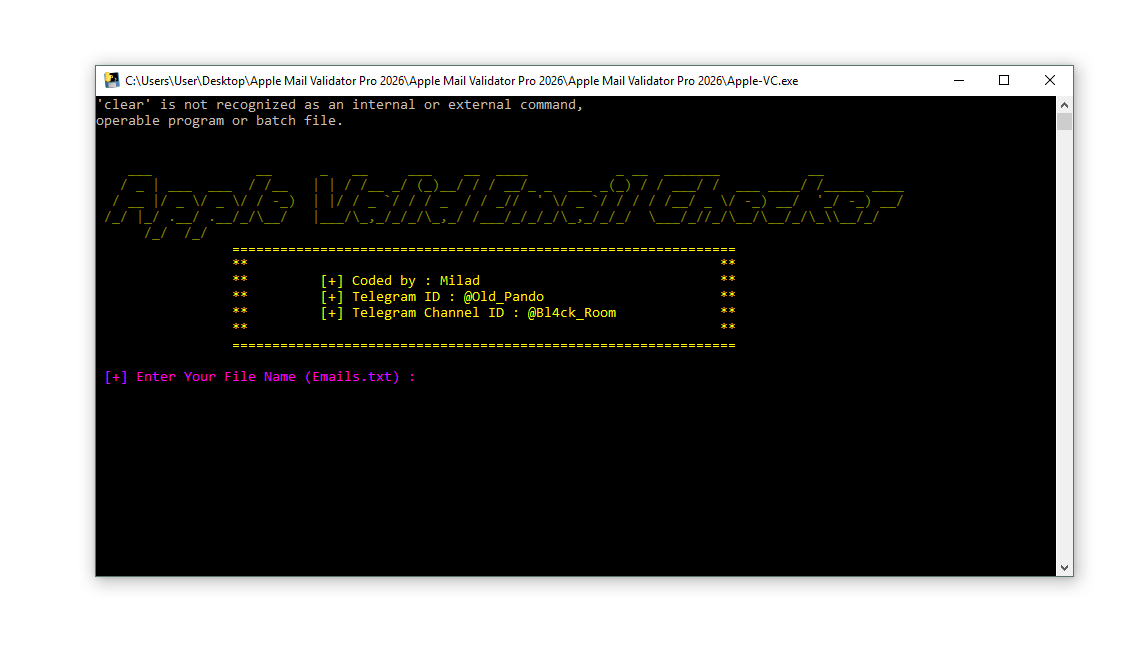
🔥 Mail Checker Pro v2.0 – High Performance IMAP & POP3 Email Verification Tool Managing and verifying large volumes of email accounts has become increasingly important for businesses, IT teams,…
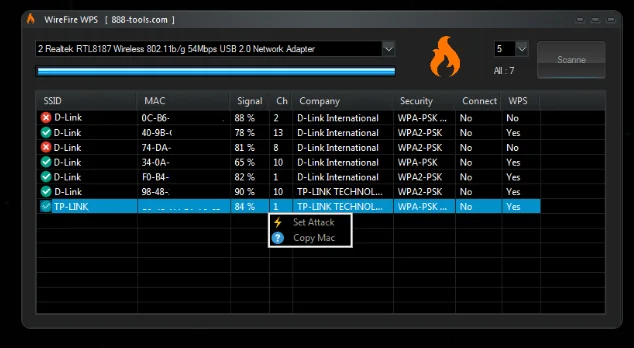
WireFire WPS 2026
🧠 📘 Introduction WireFire WPS 2026 | Hack any wifi password In the modern digital era, Wi-Fi networks are a critical part of everyday life. From homes to businesses, secure…
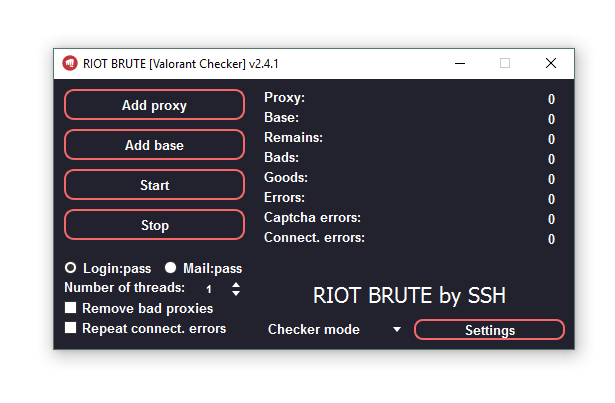
Riot Brute 2025
📌 🧠 What is Riot Brute 2025? Riot Brute 2025 is a specialized Windows-based software designed to process and validate large sets of login credentials (combolists) for Valorant accounts. It…
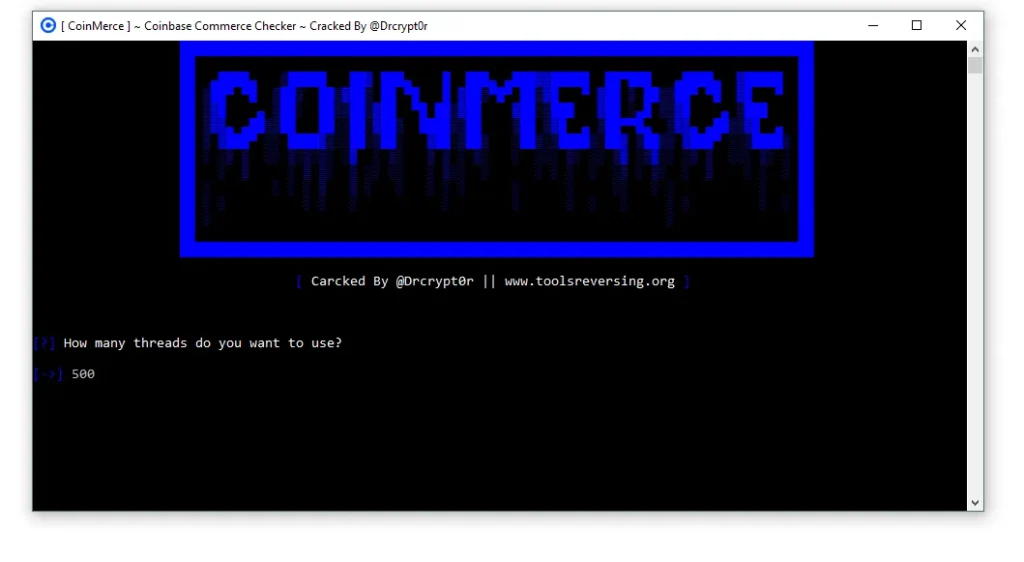
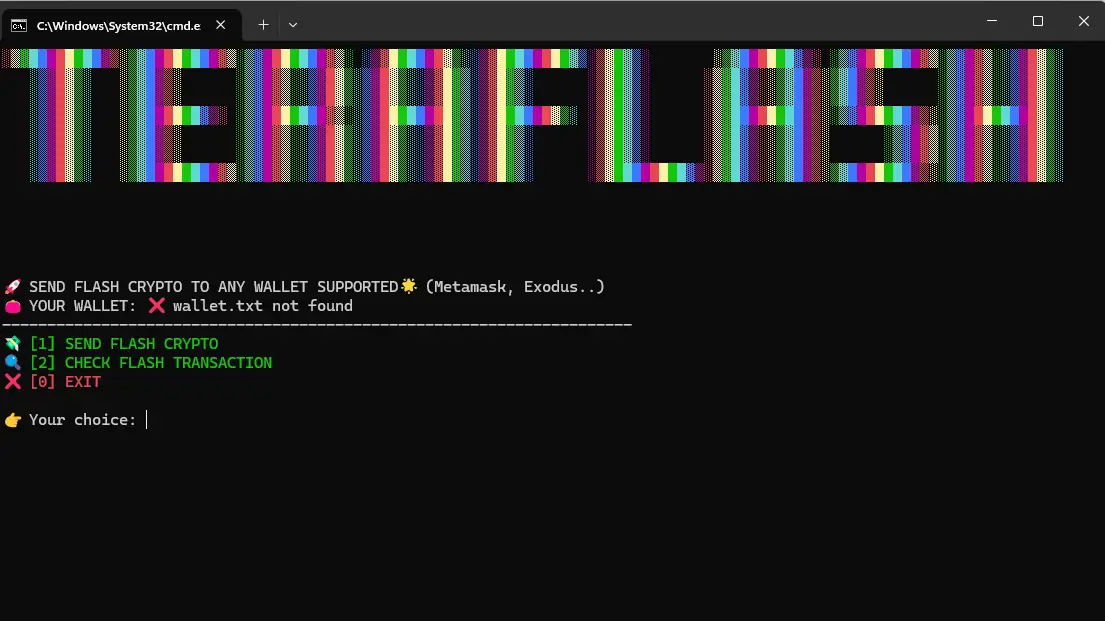
CoinMerce 2026 Cracked
🔐 CoinMerce 2026 Cracked Tool – Complete Security Analysis The rapid expansion of the cryptocurrency market has created new opportunities for traders and investors worldwide. However, the increasing popularity of…
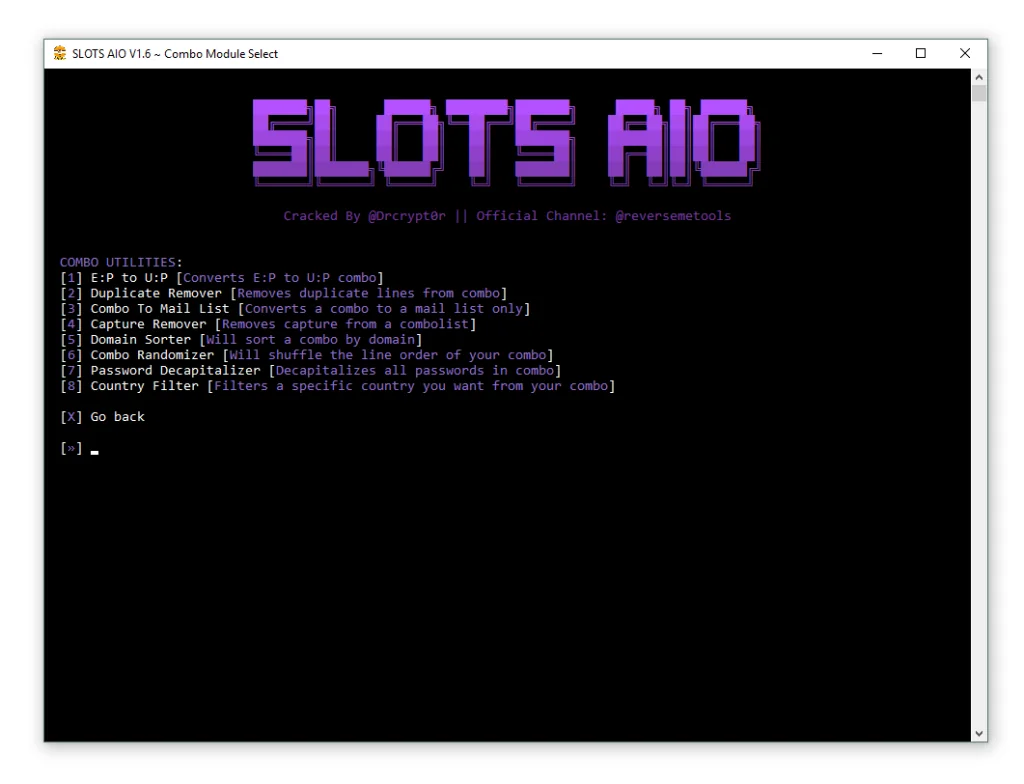
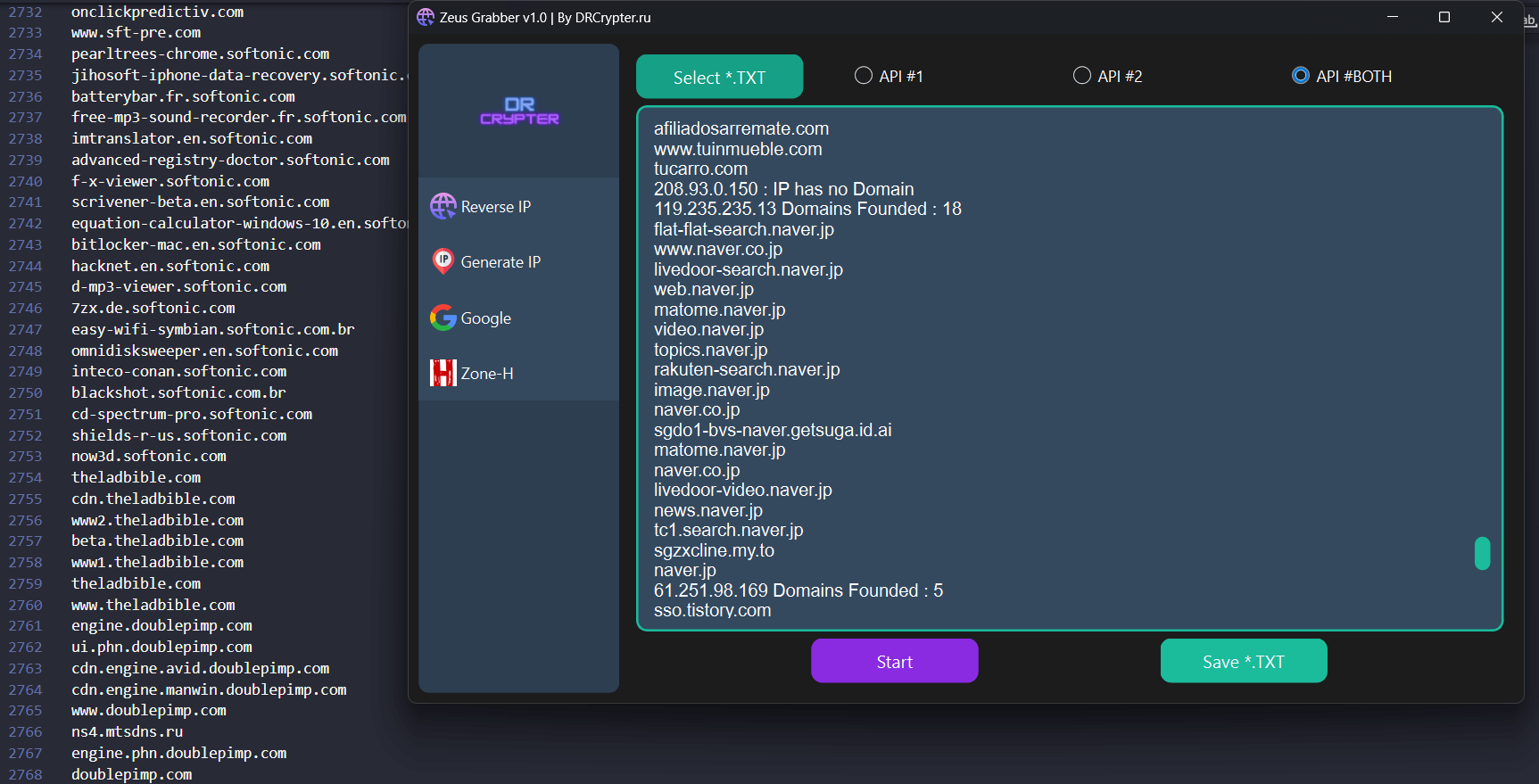
Slots AIO Checker 2026
🔍 What is Slots AIO Checker 2026? Slots AIO Checker 2026 is marketed as an “All-In-One” automated account checking tool. It reportedly supports dozens of platforms across AI services, financial…
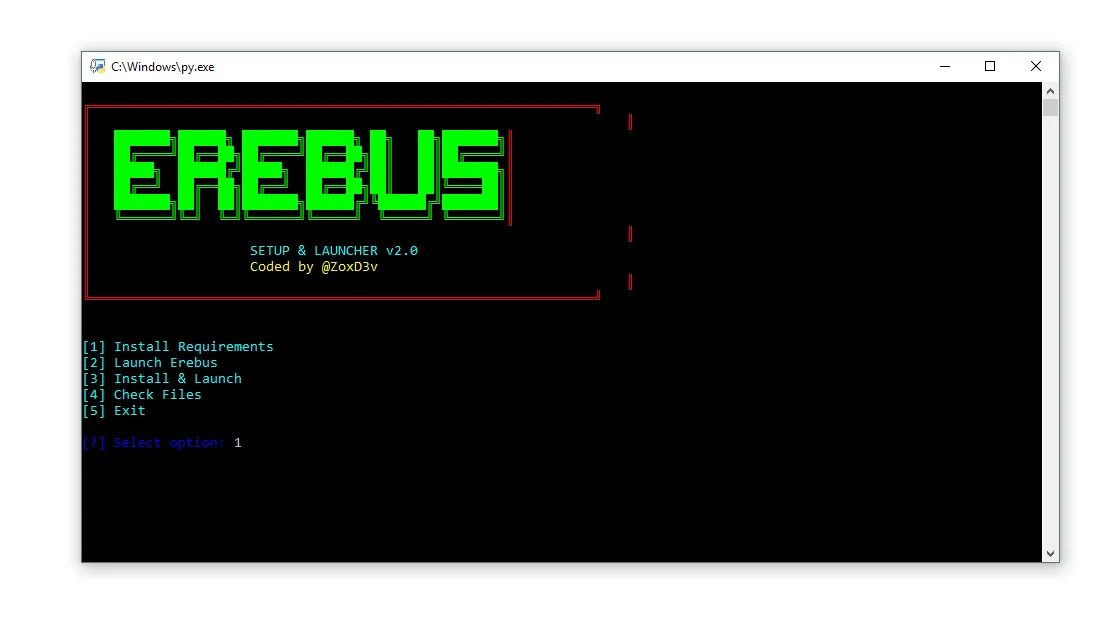
OnlyJuice Checker 2026
OnlyJuice Checker 2026 – Complete Feature Breakdown & Performance Review Introduction OnlyJuice Checker 2026 is a modern SMS checking and capture tool designed for users who need fast processing, organized…